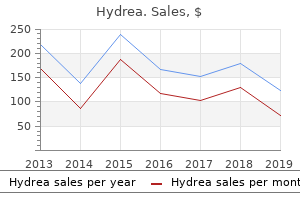
Hydrea
"500 mg hydrea fast delivery, medicine to stop contractions".
By: F. Iomar, M.B. B.CH. B.A.O., Ph.D.
Program Director, New York Medical College
Obviously symptoms after hysterectomy buy hydrea online from canada, he chose Gothic fiction as an answer to symptoms 9 days past iui cheap 500mg hydrea overnight delivery his growing family obligations medicine valley high school buy hydrea pills in toronto, as his financial situation had been worsened by the failure of the church to award him a living wage. On the down side, an evaluation in London Magazine declared the creator a misanthrope and warned that keen Gothic writing against religion and society may trigger malcontents to turn vague grumblings into crime. Melmoth the Wanderer broke new ground within the genre by abandoning extremes of lust and fantastic supernatural elements for a extra realistic examination of the dark corners of the human psyche. He interrupted his study at regulation college to enlist within the army and struggle within the FrancoPrussian War. His first success was "Boule de Suif" (Butterball, 1880), an ironic story a few ladies who agrees to sex with an enemy for the sake of ungrateful strangers. His stories ranged from comedian macabre in "La Main" (The hand, 1883) to the erotic obsessive in "La Chevelure" (The gold braid, 1884) and ethical derangement in "Moiron" (1887), the story of a instructor who punishes God by murdering students. The story ends with a realization that suicide is the one escape from the macabre. Ironically, the creator himself attempted suicide, however failed and spent the ultimate 19 months of his 43 years in an asylum. In Reflections in a Golden Eye, McCullers expands on hostility and masochism arising from disjointed loves. In each novels, she builds a pervasive unease from loneliness, fights, body dismemberment, and social and sexual displacement. Vallery (1792), was revealed in England, a critic for Monthly Review denounced the fashion as infantile for its perception within the miraculous. At the outset, she introduces the idea of sanctuary to criminals who search shelter on hallowed ground. Faustus (1810) capitalized on medieval legends, notably the phantom horseman, ghost ship, demon hunter, and the alchemist keen to promote his soul to Satan in trade for energy and knowledge. Author Robert Burton probed the subject totally within the Anatomy of Melancholy (1621), a study of psychic despair and its antidote. The textual content influenced readers and students and promoted curiosity within the subject among the many romantic poets in later years. Before Theodore, a surviving suitor, can settle for Isabella as a bride, he converses at size with her and concludes that "he may know no happiness however within the society of one with whom he may endlessly indulge the melancholy that had taken possession of his soul" (Walpole, 110). Aubert family and notes that the daddy enjoys an lively family life however retreats into solitude at twilight and mourns the deaths of his two sons, who expired in infancy. In his youth, the Russian romantic Mikhail Lermontov reflected a preoccupation with craving and doomed, bittersweet romance. At age 14, he wrote the first draft of the Demon (1840), the quaint story of a fallen angel who views earth as a prison. In a narrative marked by exotica, the wanderer, banished from heaven, woos Tamara, a bride-tobe, with worshipful, rhapsodic love. The dramatic state of affairs, set at a remote convent within the rugged Caucasus Mountains of Georgia, concludes with a fiery kiss, which kills the earthling and sends her straight to heaven for her martyrdom by intimate contact with the soulful demon. The melancholy ballad inspired sketches, paintings, stage drama, and, in 1875, the Demon and Tamara, a three-act opera by Anton Rubinstein. Reduced in grasp and vision from the lack of a hand and eye, he recedes right into a woeful cloud, a self-punishing funk that destroys his peaceful contemplation of the lawn at Ferndean. In the current century, Virginia Renfro Ellis built on postCivil War melancholy within the Wedding Dress (2002), the story of Southern widows coping with loss and witnessing the return of ghost soldiers along country roads. In- melodrama 229 stead, his autobiographical plot opens in Dublin, within the fall of 1816. The pervasive savagery of the wanderer symbolizes the evils and corruption that hang-out humankind, each on the geographical landscape and the internal terrain of the mind. The demon calls for a terrible, unavoidable punishment for overreaching human boundaries, first within the sea, then within the nether reaches. In a fearful vision, the wanderer sees himself on the lip of a precipice where an unseen pressure flings him to perdition. Maturin expands on damnation with powerful imagery: "The upper air (for there was no heaven) confirmed only blackness unshadowed and impenetrable-but, blacker than that blackness, he may distinguish a huge outstretched arm, that held him as in sport on the ridge of that infernal precipice" (Maturin, 409). The descent ends with a succession of stop-motion pictures: "He fell-he sunk-he blazed-he shrieked! The genre avoids explanations of motivation and logic to consideration to} inflated pathos, 230 melodrama thrills, wickedness, violence, and Gothic horror. Nineteenth-century melodrama supplied relief for pent-up Victorian emotions by its lack of restraint, each in word and deed.
Diseases
- Williams syndrome
- Polycystic kidney disease, infantile type
- Carbamoyl phosphate synthetase deficiency
- Rheumatoid vasculitis
- Molybdenum cofactor deficiency
- Aase Smith syndrome
Hosts that allow guest accounts and assist trusted hosts should be isolated from other hosts if possible symptoms 39 weeks pregnant hydrea 500mg sale. Security procedures should specify how this software program is installed and stored current medical treatment purchase generic hydrea line. Users should be encouraged to treatment 11mm kidney stone best purchase hydrea log out of their classes with servers when leaving their desks for long periods of time and to turn off their machines when leaving work, to shield in opposition to unauthorized individuals walking a lot as} a system and accessing services and applications. Automatic logouts can also be|may also be|can be} deployed to routinely log out a session that has had no activity for a period of time. It should be rigorously deliberate and carried out and never compromised by users putting in their own wireless entry points. Securing Wireless Networks Wireless networks are gaining widespread reputation in enterprise campus networks, at department offices, and in residence offices. Most organizations assist the will increase in productiveness and employee satisfaction that wireless networking provides but on the same time are involved concerning the safety risks, as they should to} be. In recent years, obtrusive holes have been discovered in the typical strategies used for wireless safety, resulting in the improvement of new strategies and models for offering safety on wireless networks. This simplifies addressing for stations that roam and also improves administration and safety. Keeping all wireless shoppers in their own subnet makes it easier to arrange site visitors filters to shield wired shoppers from an attack launched on the wireless network. Keep in thoughts that safety necessities for wireless users differ with kind of|the type of} user. Guests who go to an enterprise would possibly want easy access to the Internet but should be prevented from accessing the enterprise network. This is totally different from the employ- 254 Top-Down Network Design ees who want wireless entry while having lunch in the cafeteria or while meeting in non-public conference rooms. All wireless (and wired) laptop computer computers should be required to run antivirus and personal firewall software program. They also needs to|must also} be often up to date with the latest operating system safety patches. Authentication takes place after a wireless consumer has positioned an entry level with a sufficiently strong signal and chosen a channel. The consumer decides which entry level is the best for entry and sends an Authentication Request body. Upon successful authentication, the consumer sends an Association Request body to the entry level. With open authentication, the consumer is always authenticated the entry level has been configured to enable open authentication. The consumer asks to be authenticated Chapter eight: Developing Network Security Strategies 255 and the entry level permits the authentication. It would possibly sound pointless to use such an algorithm, but open authentication has its place in 802. Open authentication is commonly used for guest entry, where it would be impractical to present users with a key. The consumer sends an Authentication Request to the entry level requesting shared key authentication. The entry level responds with an Authentication Response containing problem textual content. Man-in-the-middle assaults, a form of inductive key derivation, are effective in 802. A server is helpful for big installations where configuring individual entry points can be difficult. This would possibly trigger a problem for users that roam with delay-sensitive devices, similar to 802. This is important for guaranteeing that the consumer talks to a certified server and never a hacker posing as a server. The server uses a one-time password or a username and password to authenticate the consumer. Data Privacy in Wireless Networks Previous sections discussed strategies for authenticating a wireless system (or the user of a wireless device).
Diseases
- Young Hugues syndrome
- Cataract microcornea syndrome
- Vitamin A embryopathy
- Ichthyosis hystrix, Curth Macklin type
- Glycogenosis type VI
- Lymphedema distichiasis syndrome
- Carnevale Krajewska Fischetto syndrome
- Epithelial-myoepithelial carcinoma
- Neuraminidase beta-galactosidase deficiency
- Dahlberg Borer Newcomer syndrome
If the actual boundary layer is known on the location of a proposed website medications you cant take while breastfeeding purchase discount hydrea, the identical boundary layer ought to be simulated medications mothers milk thomas hale cheap hydrea express. If not medicine 2015 cheap hydrea, the maximum speed at 30 ft altitude additionally be} measured or estimated and the boundary layer is structured according to the the place u is the imply velocity at height z and u, ~ imply velocity at reference height. The dynamic strain used for ~ d u c i n g forces and moments to coefficient the form additionally be} taken as a mean value over the mannequin, the worth famous on the center of the mannequin, or free stream q. It must, in any case, be clearly and unequivocally defined or the information are useless. These tunnels have the characteristically long test sections that allow easier manipulation of the properties of the incoming profiles and turbulence features. Geometric Scale Geometric scale is influenced by the wind modeling nicely as|in addition to} the general size of the wind tunnel. It is fascinating to acquire equality of the ratios of building size to roughness length of terrain, boundary layer thickness, and integral scale of the longitudinal element of turbulence. Blockage of the tunnel cross part is generally held under 10% and is preferably held to about 5%. Qpical scales used are within the range of 1: 300 to 1: 600 for large buildings and all the way down to} 1: 100 or much less for smaller constructions for which surface layer simulation only is required. Speed Scale and Reynolds Number the wind tunnel simulation kind of} always at very a lot smaller than full-scale Reynolds number. The simulations are useful representations of the full-scale flows for two reasons. First, the affect of excessive turbulence depth is to reduce the Reynolds number dependence. Second, the standard shapes of buildings, bridges, and the like yield flows may be} much less depending on Reynolds number than typical car shapes. Reynolds number results are strongest when the places of transition and separation vary with Reynolds number. If rounded shapes are a part of} a structure, then some schemes such as roughening of the surface are generally used. If the mannequin used is elastic, then dynamic parameters affect the choice of flow speed. Terrain Effects Information on flow charactefistics over selection of|quite a lot of|a wide range of} terrain is on the market to use in organising flows. Topographic fashions in scales ranging from 1: a thousand to 1: 5000 can be utilized for analysis of results on the flow subject. The data from such a simulation can then be utilized in organising a flow mannequin at a bigger scale for building or different structure simulations. Effects of Nearby Buildings and Topography Significant neighboring buildings, constructions, and topographic features ought to be modeled if only with block-type illustration. This sometimes consists of significant features out to 1000-2000 ft from the main structure of curiosity. The flow is influenced in this case by having the stagnation level a lot greater than can be the case in a more open setting. Cases that contain the dynamics of bigger sections of the structure, if it is elastic, may require unsteady therapy. For local pressures measured on a inflexible mannequin to predict local panel loads, a quasi-static therapy is valid. The structural responses of those small&bsystems &faster than the power containing frequencies of the atmospheric fluctuations. The instmmentation, nevertheless, must have have} suficiently excessive bandwidth capability to precisely track the time-varying pressures ensuing from the incoming turbulence constructions. Significant tubing lengths are difficult to avoid, so care have to be taken in assessing the results on the measurements. It is necessary to carry out preliminary assessments to anticipate the areas most likely to encounter peak results. Additional azimuthal points are usually needed for directions near those that exhibit essentially the most important behavior. Panel wind loads are obtained by integration of the pressures over the areas of curiosity. Various means of implementing such integrations utilizing pheumatic averaging have been utilized. These have the advantage of requiring fewer transducer readings, but they have to be fastidiously analyzed and validated for every implementation.